This site provides information using PDF, visit this link to download the Adobe Acrobat Reader DC software.
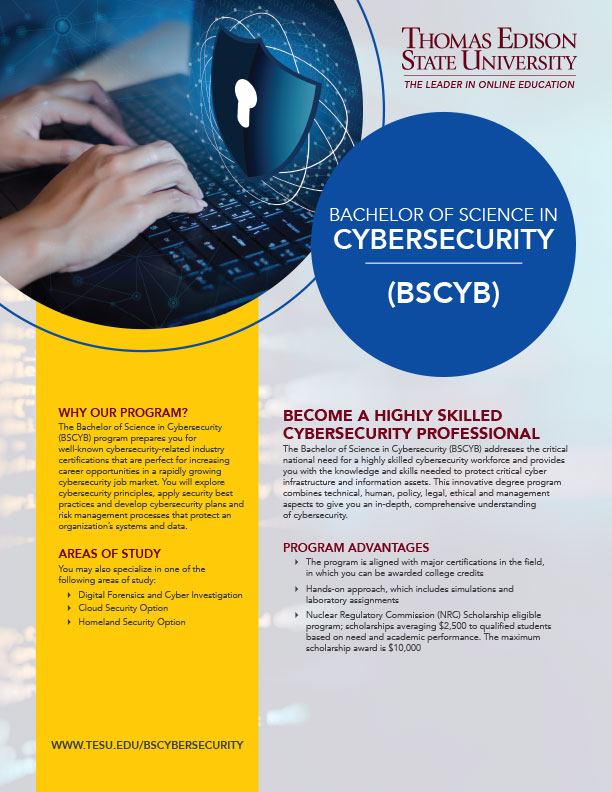
Bachelor of Science in Cybersecurity
The Bachelor of Science in Cybersecurity addresses the critical national need for a highly skilled cybersecurity workforce and provides you the knowledge and skills needed to protect critical cyber infrastructure and information assets. This innovative degree program uses an interdisciplinary approach that draws on solid technical as well as relevant human, policy, legal, ethical and management aspects needed to protect critical information infrastructure. In addition, the program prepares students for well-known cybersecurity related industry certifications that are perfect for increasing career opportunities in the current rapidly growing cybersecurity job market.
Learning Outcomes
In addition, graduates of the Cybersecurity program will possess the skills and knowledge required to:
- Assess and apply cybersecurity principles, tools and methods to defend information systems against cyber threats.
- Protect an organization's critical information infrastructure by applying cybersecurity design best practices and technologies to prevent and mitigate cyberattacks and vulnerabilities.
- Design, implement and administer networks in a secure manner by integrating network defense technologies, monitoring tools and measures.
- Apply security best practices to install, configure and manage modern operating systems.
- Implement fundamental security principles and techniques in developing secure programs.
- Apply database security models and best practices in the design and development of database management systems.
- Analyze and navigate policy, legal, ethical and compliance aspects of cybersecurity.
- Develop cybersecurity plans, programs and risk management processes to protect an organization’s systems and data.
Leverage Your Training
Have you earned acquired college-level technical expertise on the job? If so, it may be worth college credit. The University also offers a variety of other ways to earn credit, including transferring previous college credits, all designed around the needs of adult learners, like you.
Degree Program Profile Sheet
 Download our degree program profile sheet for an overview of our BS in Cybersecurity program.
Download our degree program profile sheet for an overview of our BS in Cybersecurity program.
Related Links
- Academic Programs Overview
- Undergraduate Programs
- Graduate Programs
- Administrative and Technical Programs
- Aviation Programs
- Construction Programs
- Cybersecurity Programs
- Electrical/Electronics Programs
- IT Programs
- Military Leadership Programs
- Nuclear Programs
- Allied Health/Health Technology Programs
- Radiation Safety Officer Course
- Graduate Admission Requirements
- Undergraduate Outcomes



 Toni M. Terry, BA
Toni M. Terry, BA